Helpful Summary
- Overview: We give a comprehensive overview of digital signature validation—what it is, why it’s important, how it works, and whether it’s something you need to be thinking about.
- Why you can trust us: We’re a leading provider of secure, compliant eSignatures for businesses across a wide range of industries—including real estate, construction, healthcare, and more.
- Why it matters: Digital signature validation is essential for maintaining document integrity, ensuring security, and achieving regulatory compliance. It prevents forgery, ensures signer authenticity, and is essential for legal and business transactions in the digital age.
- Action points: Implement digital signature validation by following SignWell’s step-by-step guide, which includes consent mechanisms, intent to sign, attribution of the signature, association with the document, and record retention, alongside best practices like protecting private keys and regular updates.
- Further research: For more e-signature solutions and insights, check out the SignWell blog.
Curious About Digital Signature Validation?
Digital signatures are an important tool for maintaining document integrity and ensuring security.
But without the tools and know-how to validate digital signatures, how can you be sure that the signature is authentic and legally binding? Don’t worry, if that’s a question you’ve been asking yourself—you’re not alone.
In this SignWell guide, we’ll be explaining exactly how to validate digital signatures yourself in a few simple steps. We’ll also offer some best practices for ensuring the security of your digital signatures, and a few alternatives to digital signatures that may better suit your needs.
Let’s get started.
Why Listen to Us?
At SignWell, we’ve helped 65,000+ businesses take control of their e-signing workflows with our easy-to-use e-signature platform.
We know the ins and outs of collecting signatures online, and we’re constantly staying up-to-date on useful trends and technologies—including digital signatures.
What Is Digital Signature Validation?
To answer this question, we need to start simple—what is a digital signature?
The short answer is that a digital signature is a mathematical technique that’s used to verify the authenticity and integrity of a digital document or message (like a signature). The process is complex, so here’s a generalized overview:
- The signer’s signature provider creates a unique “hash” of the document or message using a cryptographic algorithm.
- The signer creates a private key that only they know.
- The hash is encrypted using the signer’s private key to create a digital signature.
- The digital signature is attached to the document or message along with a public key.
Digital signature validation is the process of determining whether a digital signature is valid.
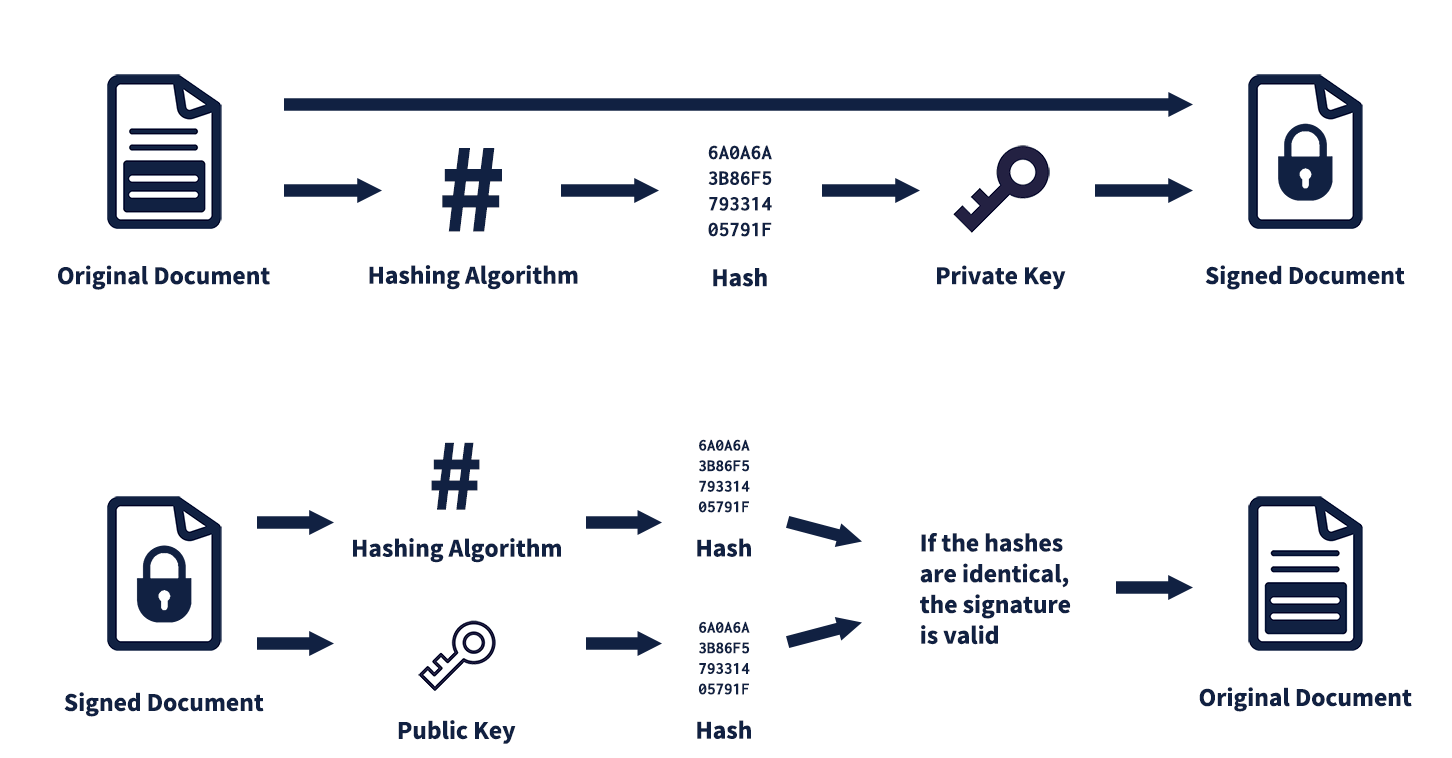
How? Using the public key that comes attached to the document or message. Anyone can use this public key to decrypt the digital signature and verify that it was indeed created by the private key associated with it.
If the decrypted hash matches the original one, then the digital signature is considered valid.
Key Components of Digital Signature Validation
To make sure everyone is clear on the concept, let’s break down the key components of digital signature validation:
Hashes & Hashing Algorithms
A “hash” is just a fancy term for a fixed-length number that uniquely represents some data. Hashing algorithms are used to create these unique numbers, which are essentially digital fingerprints of the original data.
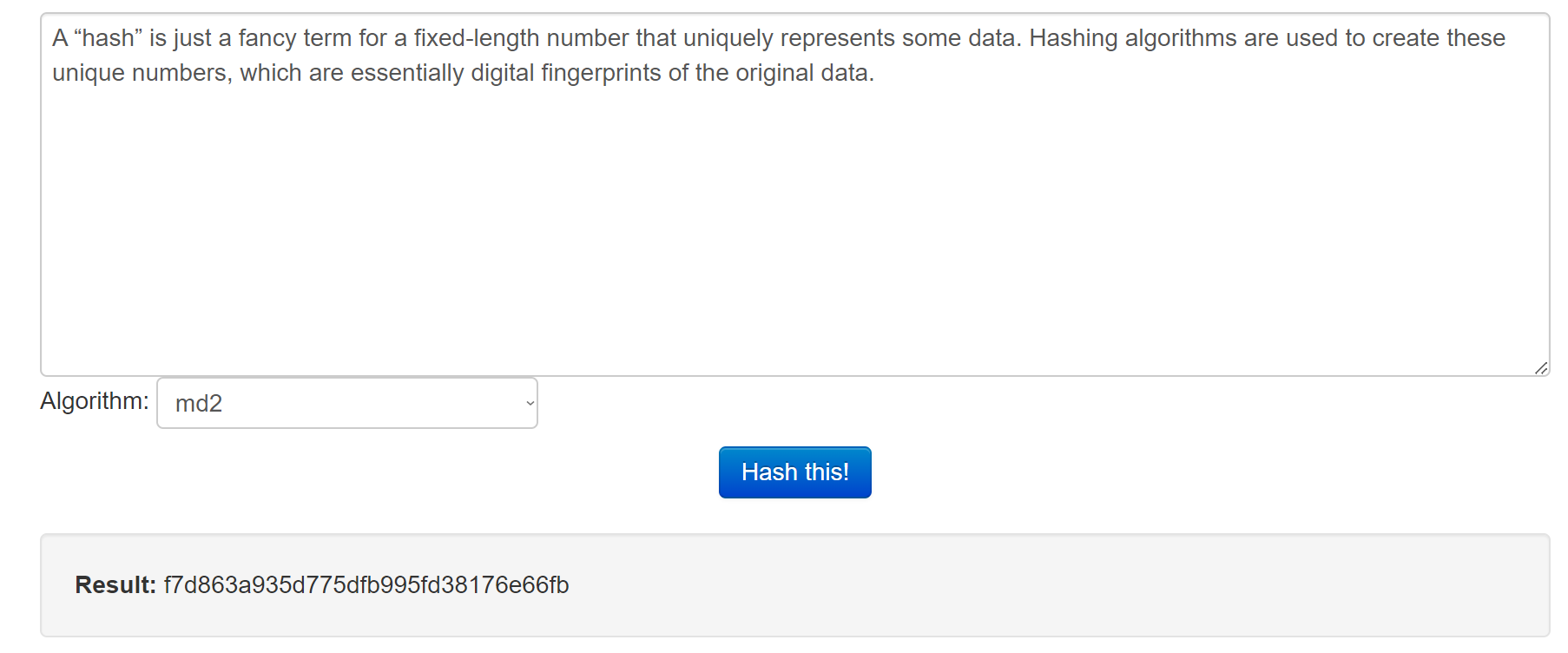
For example, the hash of the previous paragraph (using the MD2 algorithm) is:
- F7d863a935d775dfb995fd38176e66fb
If you decode this hash, you’d then be able to generate the original data.
Public & Private Keys
Public and private keys are tools used to make digital signatures secure. These keys are two different numbers that work together in a special way—data encrypted with one key can only be decrypted with the other key.
Here’s an overview:
- Private Keys: The private key is kept secret by the signer. It might be a PIN, a password, or something else that only the signer knows. It is then used by the digital signature provider’s protocol to encrypt the hash.
- Public Keys: The public key is shared with others and can be used to verify the digital signature. This key is mathematically linked to the private key and can be used to decrypt the encrypted hash.
There are some great interactive demos out there that let you play with public/private key encryption if you want to learn more.
Certificate Authorities
A certificate authority (CA) is an entity that issues digital certificates to verify the identity of individuals or organizations online. This allows users to trust that a digital signature is authentic and belongs to the correct person or organization.
CAs use specialized software and processes to ensure the security and validity of these certificates.
How to Validate Digital Signatures
Step 1: Open the PDF Document
The first step towards validating a digital signature is to open the PDF document where the signature appears. For the remainder of this guide, we’ll be explaining the steps using Adobe Acrobat—but it’ll look similar in any tool that can validate signatures.
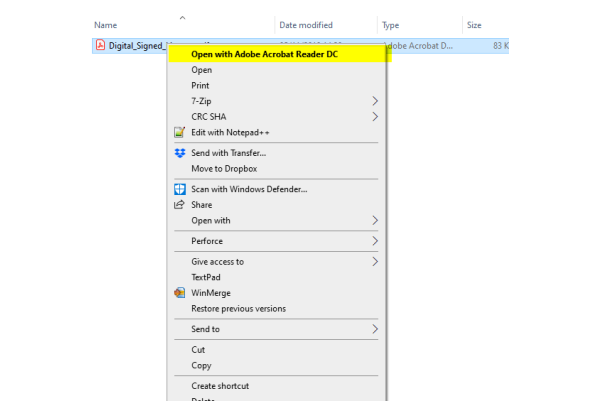
So, open the PDF file containing the digital signature using the software of your choice by right-clicking the file and selecting “Open with…” followed by the name of the tool you’ll be using.
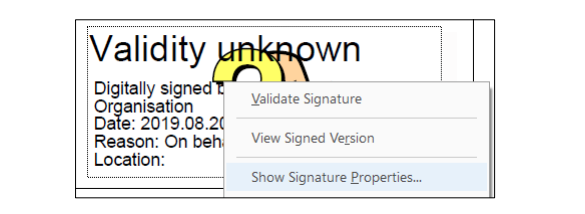
Step 2: Select the Signature
Next, find the signature in the document by scrolling through the pages or using the search function.
Once you’ve located it, you’ll need to interact with the signature. In Adobe, this is pretty intuitive—just right-click on the signature block and click “Show Signature Properties.” The key is right-clicking.
If you simply click, all you’ll see is the standard context menu.
If you’re using a different tool, consult the support documentation for guidance on how to interact with digital signatures. Depending on your software, it could involve using specific options like “Certify with Visible” (if visible signatures are used).
Step 3: Check Signature Validation Status
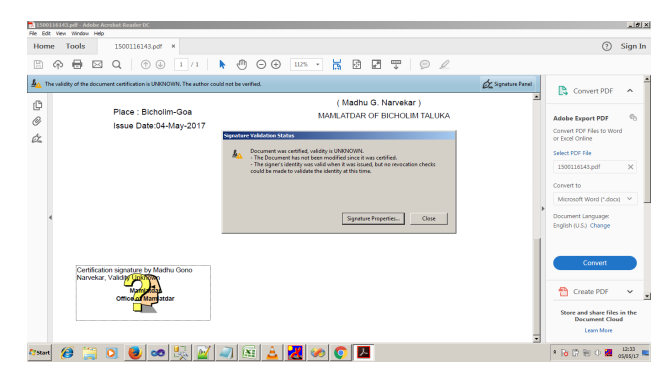
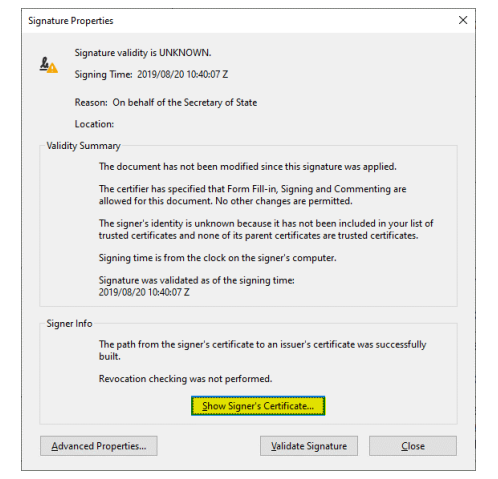
After right-clicking the signature and clicking “Show Signature Properties,” expect a dialog box or a window to appear. This is the “Signature Validation Status” window. If the signature status is initially validity unknown (or similar), right-click on the corresponding icon.
Click the option to “Validate Signature.” The Signature Validation Status window will display important information— you can see an example below:
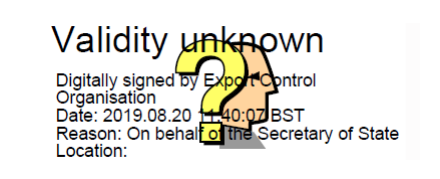
Look for compliance status messages and potential warnings about the signature’s validity.
Step 4: View Signature Properties
For a more comprehensive understanding of the signature and its validity, explore the option labeled “Signature Properties” or “Validate Signature,” depending on the software you’re using. This detailed view should present a validity summary, information about the signer’s certificate, and any legal restrictions associated with the signature.
In Adobe Acrobat, click on the signature field to view the initial details, and then the “Show Signature Properties” button.
In the Goa Online PDF, you can click on the “Signature Properties” button and then “Show Signers Certificate” to check signature properties.
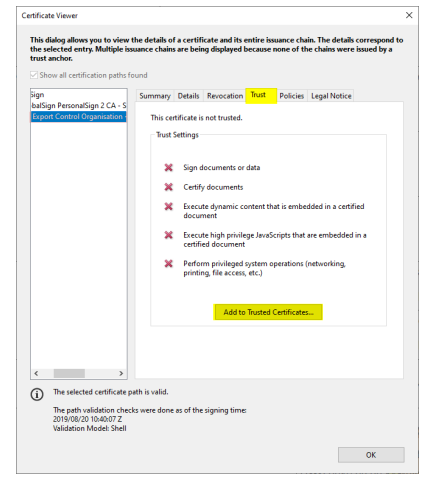
Step 5: Verify the Signature Certificate
Within the signature properties, look for the option to “Show Signer’s Certificate.” This step allows a thorough review of the certificate used for signing, including scrutinizing trust settings and confirming the certificate’s validity.
Step 6: Check Document Integrity
Confirm that the document has not been altered post-signing. The validation process checks the content to ensure it stays unchanged, maintaining the document’s integrity.
To do this, go to the “Tools” menu and select “Protect Document.” Then, choose “Validate Current Document” and click “OK.” The system will automatically verify the document’s integrity and inform you if any changes have been made since it was signed.
Step 7: Verify Certificate Trust Settings
In certain scenarios, it might be necessary to adjust trust settings for the signer’s certificate. This step involves adding the certificate to a list of trusted identities, which ensures the signer is duly recognized as a legitimate entity.
Step 8: Validate Timestamp (If Applicable)
Thorough verification is important for digital signatures with timestamps. Confirm the timestamp details to determine the exact signing date and time of the document. This verification step is especially important when precise timing is essential or when the certificate of a signer expires at a later date than the document was signed.
Step 9: Contact the Signer (If Necessary)
When unsure about the signature’s validity or if discrepancies arise, it’s important to proactively communicate with the original signer. Direct contact helps verify and gather more information effectively.
Step 10: Repeat for Additional Signatures (If Necessary)
When a document has multiple signatures, it’s important to validate each signature separately. This thorough process guarantees the document’s authenticity and integrity, boosting confidence in all attached signatures.
Best Practices in Implementing Digital Signature Validation
Don’t Over-Rely on Digital Signatures
Digital signatures are an important tool—but they aren’t necessary for every document. And beyond that, they can actually harm your business by slowing down processes and increasing turnaround times.
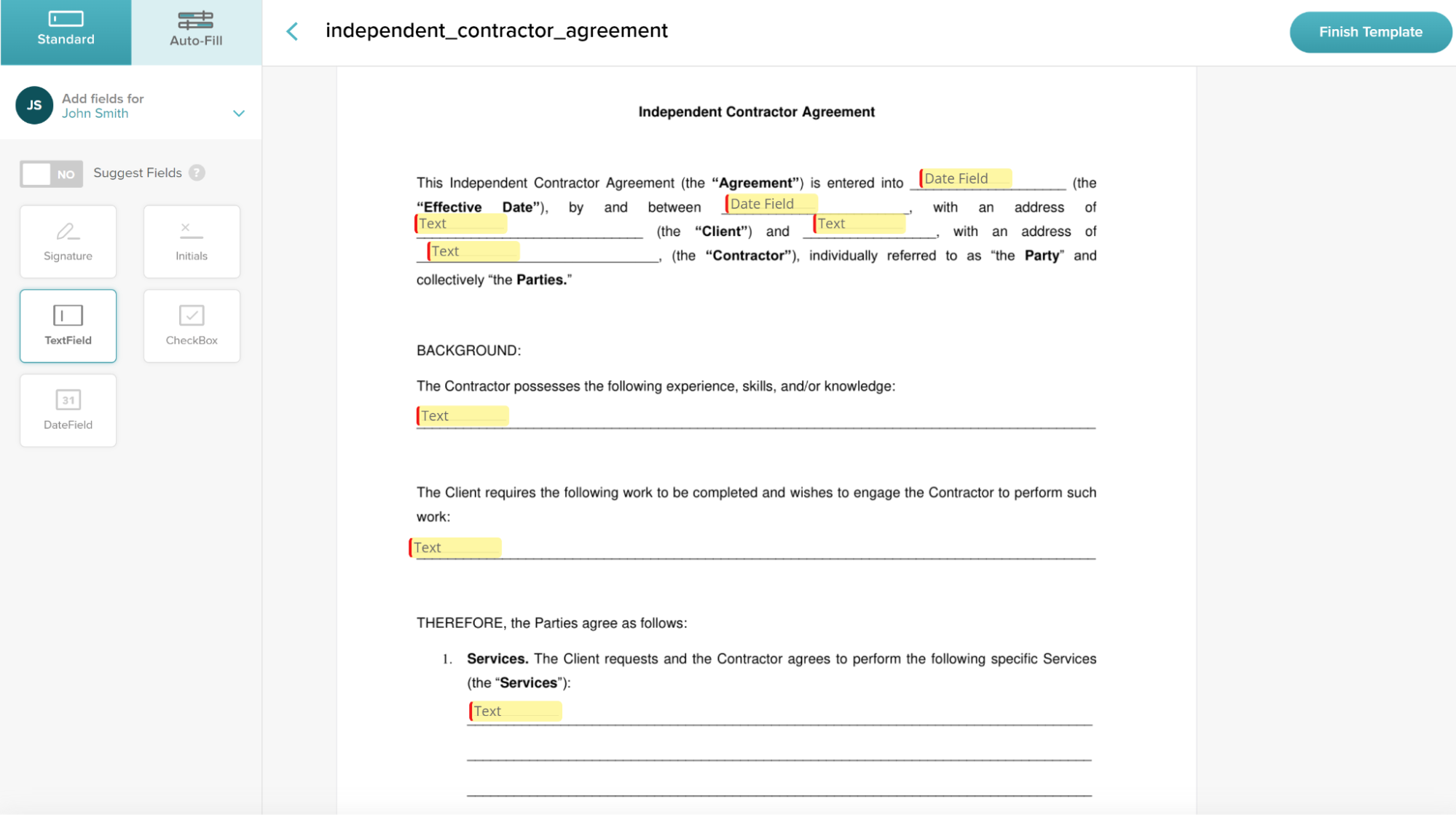
Simple, mid- to low-risk documents may not require a digital signature. E-signature tools like SignWell offer a balance of security and convenience that boosts workflow efficiency while still collecting legally binding signatures.
How do we protect your documents? Here’s a quick overview of our security features:
- Audit Trails: Access detailed logs covering document actions, IPs, and timestamps.
- Encryption: Protect sensitive information with secure encryption at rest and in transit.
- Compliance: Comply with ESIGN, eIDAS, GDPR, SOC 2 Type II, HIPAA, and more by default.
Beyond that, we offer tons of features for speeding up your e-signing process, like automated reminders, a document management dashboard, customizable templates, and a drag-and-drop editor.
The bottom line—digital signatures are useful, but on an as-needed basis. Simple, electronic signatures are great for speeding up personal workflows while maintaining legal compliance. There are also tools like Advanced Electronic Signatures (AES) that offer a higher level of security and compliance.
Protect Private Keys
If hackers or unauthorized users gain access to your private keys, they could potentially sign documents on your behalf without your knowledge. To prevent this, use a combination of hardware and software security measures to protect these keys.
For example, you could:
- Store your private keys on a hardware token or USB drive that requires a password to access
- Use multifactor authentication, like biometric scans or one-time passwords
Regularly Update Algorithms and Keys
If you really want to ensure the security and integrity of your digital signatures, it’s important to regularly update the algorithms and keys used for signing.
What we mean by this is:
- Changing the algorithm used to generate hashes and encrypt data
- Generating or choosing new private keys and replacing the old ones
That first point might sound complicated, but it’s really quite simple (depending on the tool you’re using). You can usually just select a different algorithm from a dropdown list or make a change in the code.
As for private keys, have employees generate new ones every so often. This can be done manually or through an automated system. It’s also important to dispose of the old keys properly to prevent any potential breaches.
Generate Audit Trails
Audit trails are essential for maintaining a record of all activities related to digital signatures.
By tracking the signatories, timestamps of signatures, and any changes made to the document after signing, organizations can ensure the accountability and integrity of their documents. In the event of any disputes or investigations, having a detailed audit trail can provide valuable insights into the sequence of events and help establish the authenticity of digital signatures.
Prioritize User Education and Training
As you may be able to tell from this guide, validating digital signatures requires some technical knowledge and understanding. It’s essential that users get educated and trained on:
- The importance of digital signatures
- How to validate them
- What to do if they encounter any issues or discrepancies
Educational resources like online tutorials, webinars, and guides (like this one!) are useful here. That said, the best training is hands-on experience. So, consider providing your team with opportunities to practice using and validating digital signatures in a simulated environment.
Conclusion
Implementing digital signature validation is an important step in securing digital documents. By adhering to best practices, organizations and individuals can guarantee the reliability and integrity of their signatures, building a trustworthy and secure digital environment.
Looking for a less tedious way to securely sign documents?
At SignWell, we offer secure, legally binding eSignatures with an industry-leading e-singing workflow that slashes turnaround times and reduces errors. With features like audit trails, encryption, and international compliance, SignWell makes signing documents easy and secure.
Sign up now for free to get started.